BYOD is not an acronym to let barbecue guests know what to bring with them. No, in fact it stands for “bring your own devices” and in the workplace it is a phrase that is becoming much more commonplace. Devices such as smartphones and tablets are costly items, meaning that many companies are unable to provide their workforce with necessary equipment or the technology that their staff might like! This is where BYOD comes in handy as employees are able to work with their own hardware.

The risks
Xpert HR say that “as many as 80% of smartphones used for work are employee-owned” which, on the face of it is saving companies a lot of money. However, there are numerous risks with BYOD, which could result in costly compensation payments or rectifications. Xpert HR lists the risks as follows:
- Security risks such as loss of confidential information
- Use of a device for work while driving or operating safety-sensitive machinery
- Inappropriate postings
- Privacy concerns
- Overtime pay issues
When an employer allows external devices or hardware into the office or to become associated with the company, there are always going to be risks. There is no way of monitoring the security of the device, or what happens to information stored on them after working hours. Confidential information could be extracted or harmful software could put an organisation’s system in danger.
Benefits
There are benefits too though, which are listed as:
- Improved employee morale if employees can choose their own technology
- More sophisticated technology than that which the employer may invest in
- Employees may take better care of their own devices.
If a device is employee owned it could be that they are looked after more carefully than something that does not belong to them. It’s possible that the device or software installed is more advanced than would realistically be affordable to the company too meaning that in effect, the company is acquiring better products.

Employee concerns
James Kendrick, writing for ZD Net highlights the concerns that employees may have regarding privacy. The privacy issues surrounding confidential company information are fairly obvious, but what may not be so apparent is that employees may also have to give up their own personal information. If there is an issue with security and management need to take a look at one of their employee’s phones, there could be an uncomfortable or embarrassing situation. James compares this to inviting your boss into your house when you’re not at home!
There are complications too when it comes to theft or damage of an employee's personal property. If they are using their own technology on company service, this may not be covered by work insurance. The problem arises as to who is responsible for covering the costs.
Outline a policy
There is a clear way to prevent difficult situations, Mark Pearce says, and that is to outline a policy. Writing for HR Bullets, Mark talks about the three specific areas that agreements need to be reached for in order for a BYOD policy to be successful. The first area that must be agreed upon is Personal Data. He says:
“Employees need to be made aware that they forfeit some of their rights to their personal data stored on such devices. Also, if connected to a workplace network, personal files such as photographs and correspondence may be mistakenly damaged or deleted by the employer.
Security is another big point of contention as if a device is lost or stolen then it is in the company’s interest to protect their data and will want to wipe any information stored. Employees must be informed in advance about the company’s intentions.
Finally, Billing and ownership should be addressed. When a device is being used for both work and personal reasons it is unclear who should foot the bill. What’s more, if an employee leaves the company, but retains their phone number on their own device, it is possible that clients may move to competitors if they are still in contact with the ex-employee through their phone number. By identifying ownership of numbers and contact details in advance no unpleasantness should occur after employment ends. There could be an awkward situation whereby an employer requests that a staff member's personal number or email address be changed.
Compliance with these rules should be reviewed on a regular basis, as well as periodic checks for security on all devices involved in the BYOD scheme. Agreements must be reached between all parties before BYOD is permitted within an organisation, and serious consideration into the consequences must be taken.
______
Sources:
HR Issues Around BYOD | Xpert HR
BYOD: Like Inviting Your Boss To Your House When You're Not Home | ZD Net
BYOD - What The Hr Department Needs To Know | HR Bullets

Written by Fiona Sanderson
Fiona is Marketing Manager at myhrtoolkit. Her areas of expertise include HR systems, productivity, employment law updates, and creating HR infographics.

 Holiday Planner
Holiday Planner Absence Management
Absence Management Performance Management
Performance Management Staff Management
Staff Management Document Management
Document Management Reporting
Reporting Health and Safety Management
Health and Safety Management Task Management
Task Management Security Centre
Security Centre Self Service
Self Service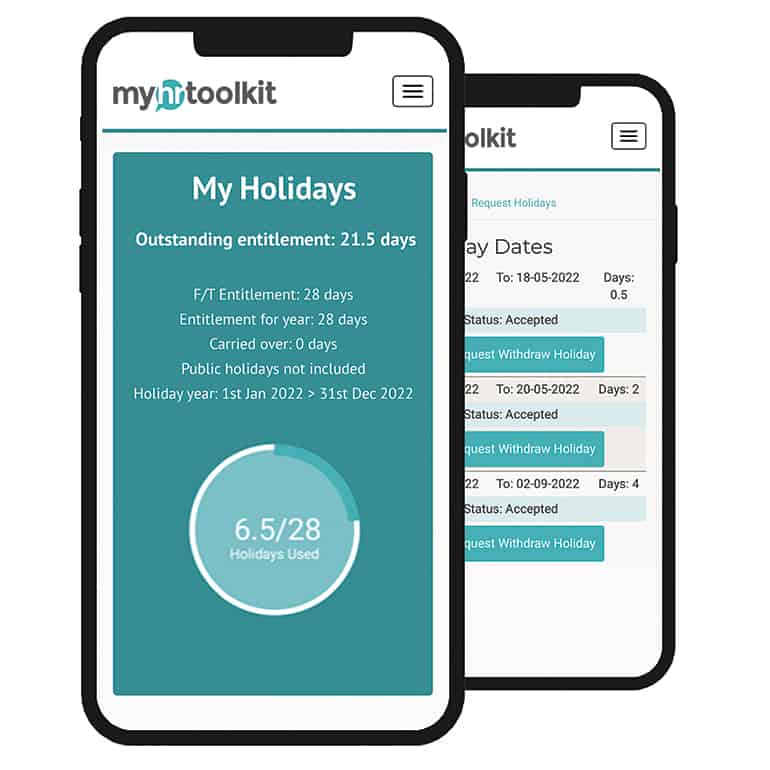 Mobile
Mobile



