If you are looking to store your important and confidential HR information in cloud-based software you may worry that your data is at higher risk because it is stored on remote servers outside of your control.
But think about it. Most of us sit at a work PC that links our hard drive content to the Internet. As a result, any content saved on your local computer or network is just as vulnerable to hacking, malware and viruses as any data you store in the cloud on remote servers.
However, while most organisations address the security of their own PC network by using good firewall and antivirus software, a good online HR software provider will have put in place a huge number of additional measures to ensure the security of your data.
What security measures do cloud based HR software suppliers take?
A good online HR software supplier will have made sure they are using a cloud hosting company that employs state-of-the-art technology to protect their servers and any information passing between them.
This can include:
Data sanitisation
This security method aims to remove any malicious data when users input information, for example on form submissions. It essentially checks user inputted data against a set of expected input and disregards anything unexpected. Sanitisation approaches can include removing unusual symbols from the inputted text to removing SQL injection attempts.
Database encryption
Encryption is one of the best ways to ensure that the information on your database remains secure. That is because it translates the data into a secret code. As a result, unless you know the secret key or password to decrypt or decipher the data, you will never be able to discover the contents of the database.
Learn more: Password security: policy and best practices for your organisation
Session hijack protection
When you login to use your online software, the time you spend on the system before logging out is called a session. Without the right protection, hackers can get into the system by using your session and view confidential data. They do this by stealing the cookie that is used to authenticate you as a legitimate user to the remote server.
There are a number of effective ways to protect against hijacking. These include generating a complicated session key, which is hard for hackers to guess or work out; matching session keys to the users’ IP address and reducing the length of time that session keys are valid for.
Industry-standard Secure Socket Layer encryption
When you login to your HR software, your browser is effectively asking your remote server to ‘open up’ and give you access to the data on your software over the public Internet. So it is hugely important that all of that data is delivered to you securely. To achieve this, your browser must request and check that the remote server has an SSL certificate. Only when the browser acknowledges it is happy with this certificate and the server sends back a digitally signed acknowledgement to start an SSL encrypted session, can the encrypted data be shared between you and the server. In this way, SSL can protect against login and password theft and preserve the security and integrity of the data you access.
Military grade encryption for uploaded documents
This basically means that the system uses the highest level of encryption to prevent hackers from viewing documents sent to the server.
This level of encryption is typically used by organisations holding hugely sensitive information, such as military establishments and banks.
A sophisticated firewall to protect the remote servers
A firewall is an important piece of software that creates a security barrier between a trusted internal network and an external network such as the Internet, which is seen as a high risk environment.
The remote server’s firewall controls both incoming and outgoing traffic based on pre-determined security rules. Traffic that does not meet these requirements is simply not allowed to pass through the firewall.
An intrusion detection and prevention system
These systems monitor network traffic and system activities to detect and block malicious attacks. This means that if, despite the huge raft of security solutions listed above, the data held on your remote server comes under attack it can be identified and blocked immediately.
Physical security
Of course, none of the above is particularly useful without the remote servers being secure from theft, fire or other types of physical damage. With this in mind, it is vital that whichever cloud solution provider your HR software company uses, they have the proper security measures and business continuity measures in place to address this area of risk.
Disaster Recovery
We all know that despite our best efforts, things break. Sometimes hard drives fail, networks collapse and databases corrupt. Your service provider should be prepared for this eventuality and have robust, tested disaster recovery procedures in place. This may include a 1-hour hardware replacement, or a 100% network up-time guarantee or a backup server hosted with another provider that can be brought online in the event of a major failure.
Learn more: How and how often should your business back up its data?
Staff training
Quite often the weakest link in any security is us. As humans, we’re not hardwired to constantly think defensively about data security. Phishing attacks make the most of this and they can be extremely successful. It is vital then that your service provider has well thought out anti-phishing security in place to ensure that your data remains safe.
Learn more: Information security and HR: creating a security-conscious culture
Security you can rely on
Hopefully you can now see that cloud-based solutions providers use far more tools to protect your data than are used for most on-premises networks. Hosting providers might well hold your data on remote servers in the cloud; but far from taking a fluffy view of security, they keep a very keen eye on threats to your data.
To find out about the security methods that myhrtoolkit uses to protect its system and your data, see our security statement or click here to find out more about our cloud computing provider.

Written by Fiona Sanderson
Fiona is Marketing Manager at myhrtoolkit. Her areas of expertise include HR systems, productivity, employment law updates, and creating HR infographics.

 Holiday Planner
Holiday Planner Absence Management
Absence Management Performance Management
Performance Management Staff Management
Staff Management Document Management
Document Management Reporting
Reporting Health and Safety Management
Health and Safety Management Task Management
Task Management Security Centre
Security Centre Self Service
Self Service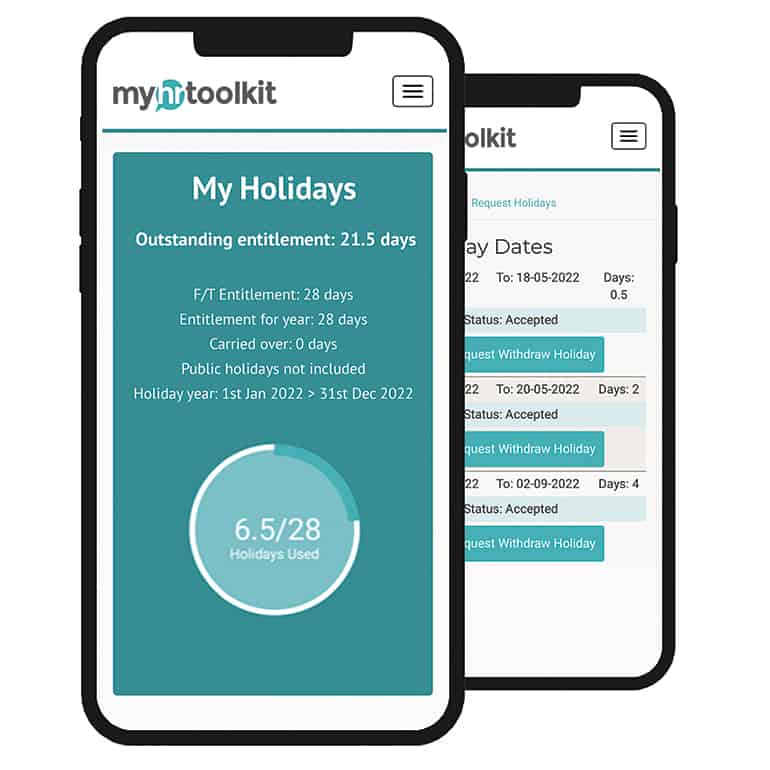 Mobile
Mobile



