Recently the news has been ablaze with a newly discovered vulnerability in OpenSSL, a popular software package that encrypts communication between websites and its users.
The “Heartbleed” bug affects hundreds of thousands of web servers all over the world, including Yahoo! and even the FBI, and allows attackers to access the encryption keys on the server and therefore see all communication with the server in plain text.
The bug was discovered by Google and Codenomicon, a Finnish security company. They revealed the bug to the world on Monday 7th April 2014, but not before passing on details of the bug to the makers of OpenSSL to allow it to be fixed before the world in general knew of the vulnerability.
It’s worth mentioning that there has been no mention of this exploit being actively used anywhere before it was made public. This means that in reality the probability of any servers being compromised by this bug prior to Monday is very small.
Here at myhrtoolkit, our servers were updated with the patched version of OpenSSL on Tuesday afternoon and we are not vulnerable to the bug.
As an extra precaution, we have also changed our security keys so that, in the unlikely event that someone did gain access to our keys, they are now useless to them.
If you are particularly security conscious, you may decide to force a reset of all employee passwords. That is something you may wish to consider with your IT department, or other IT advisers, having digested the available information online.
If you want to know more about the Heartbleed bug, head to the Heartbleed website.
Related posts
Information security and HR: creating a security-conscious culture
Why should you choose an ISO 27001 certified HR software provider?

Written by Kit Barker
Kit is myhrtoolkit's Chief Technology Officer and a company director for myhrtoolkit who leads the technical team in developing the system. On our blog he shares specialist knowledge and tips around data security and company culture.

 Holiday Planner
Holiday Planner Absence Management
Absence Management Performance Management
Performance Management Staff Management
Staff Management Document Management
Document Management Reporting
Reporting Health and Safety Management
Health and Safety Management Task Management
Task Management Security Centre
Security Centre Self Service
Self Service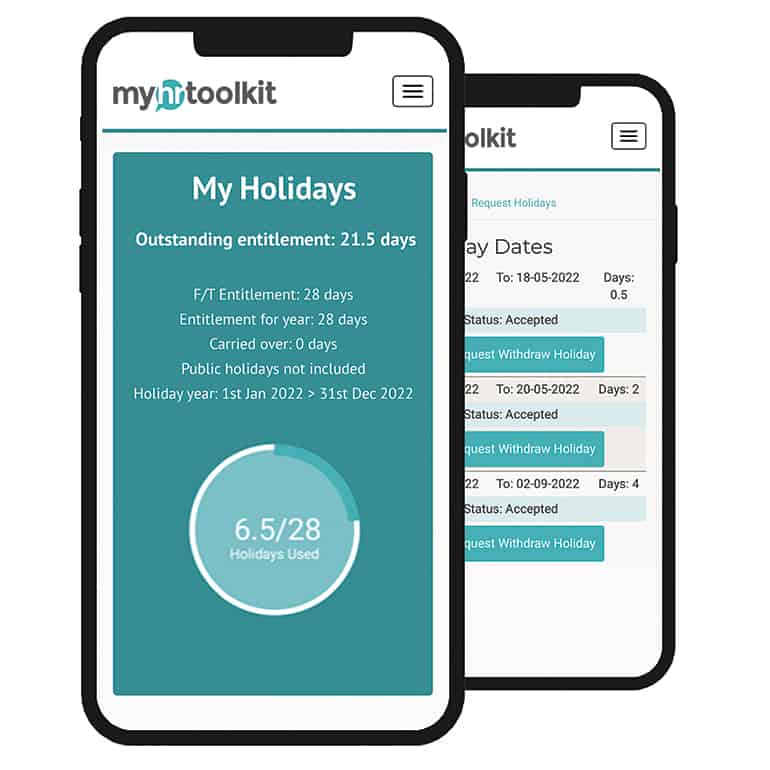 Mobile
Mobile



