Is your information security awareness training effective for your employees and your business? Learn more with this guide from myhrtoolkit's Chief Technology Officer, Kit Barker.
What is information security awareness training?
The threats to your data are constantly evolving; new threats emerge, old ones cease to be relevant, and best practice changes. Information security awareness training is a great way of ensuring people are kept up to date with the current threat landscape.
What makes information security awareness training effective?
When delivering any sort of training, it is important to be aware of the training goals. With information security awareness training, the goal is to provide your team with the knowledge they need to keep your information safe. That might seem obvious, but it is surprisingly easy to deliver ineffective training.
For example: we all know that clicking links or opening attachments in emails can be dangerous, but any training where you tell people to not do these things is going to be highly ineffective. Why? Because people need to do those things to do their job. It isn’t reasonable to expect people to act in this manner.
This is an example where “best practice” can be at odds with the reality of being productive (for clarity – this is not best practice).
To be effective, your training needs to be practical and achievable. The only way people will follow good security practices and be productive is if these two goals are aligned.
Explain the “why” not just the “how”
As mentioned at the start of this article, the threats to information security are many. It’s simply not feasible to cover all threats and appropriate responses in training sessions. Effective training needs to be practical, but it should also focus on some of the theory too.
Let’s take password security as an example. You might train people to always create strong passwords that are at least 16 characters long, unique, and containing letters, numbers, and special characters. That is a good thing. Sadly however, many online services don’t allow passwords that long, or can’t cope with special characters. In this situation, how should a user best create a strong password? Without taking the time to explain how passwords work, and how they’re compromised, it isn’t easy for the user to make a well-informed decision.
Align training and policies
If you’ve seen any of my previous articles or webinars, you will know that I love a good policy! When delivering any training, especially if this is outsourced, you need to ensure that it is aligned with, and supports your policies. Policies can be seen as informing people what you require them to do, and training is providing the knowledge as why and how they should do it.
Little and often
To be effective, your training should be delivered in manageable chunks and happen frequently. Trying to cram too much into your training will generally overload people, especially if you’re delivering training to non-technical people.
Having frequent points of contact with your staff also allows you to be responsive to the latest threats and keep your advice current. The field of cyber security moves so fast that annual training is likely to leave you exposed.
How do you know your training is effective?

Even if you follow all this advice, how can you be sure that your security awareness training is effective?
Tracking which team members have completed training is essential to ensure everyone is doing appropriate training but it can’t tell you if that training is effective. For this, you’ll need to use some metrics.
Phishing campaigns
With email and phishing being one of the main attack vectors, running your own phishing campaigns can provide you with a lot of great information about who’s not following best practice and is clicking links they shouldn’t be. Running these repeatedly will (hopefully) show you how effective your training is and show you who needs extra training.
Password security
Many password managers will provide you with information about who’s following best practice and using unique, strong passwords and who isn’t.
Security incidents
The main, and arguably the only important metric, is how many security incidents you have. To be clear, everyone will encounter many security incidents throughout the normal course of business. If you are reporting no incidents, then almost certainly your reporting is wrong and needs fixing quickly.
You should encourage your team to be as open as possible about all security incidents, whether that’s clicking a link they shouldn’t have, or opening a dodgy attachment, or even entering their password into an insecure site. Everyone makes mistakes and it is vital that people feel they can own up to them because if they hide it your risk increases exponentially.
Finally, remember that security is a process, not a product. Security awareness takes time and a lot of effort but is the best way to keep your information secure. Stay safe.
Read more from the myhrtoolkit blog
Information security and HR: creating a security-conscious culture

Written by Kit Barker
Kit is myhrtoolkit's Chief Technology Officer and a company director for myhrtoolkit who leads the technical team in developing the system. On our blog he shares specialist knowledge and tips around data security and company culture.

 Holiday Planner
Holiday Planner Absence Management
Absence Management Performance Management
Performance Management Staff Management
Staff Management Document Management
Document Management Reporting
Reporting Health and Safety Management
Health and Safety Management Task Management
Task Management Security Centre
Security Centre Self Service
Self Service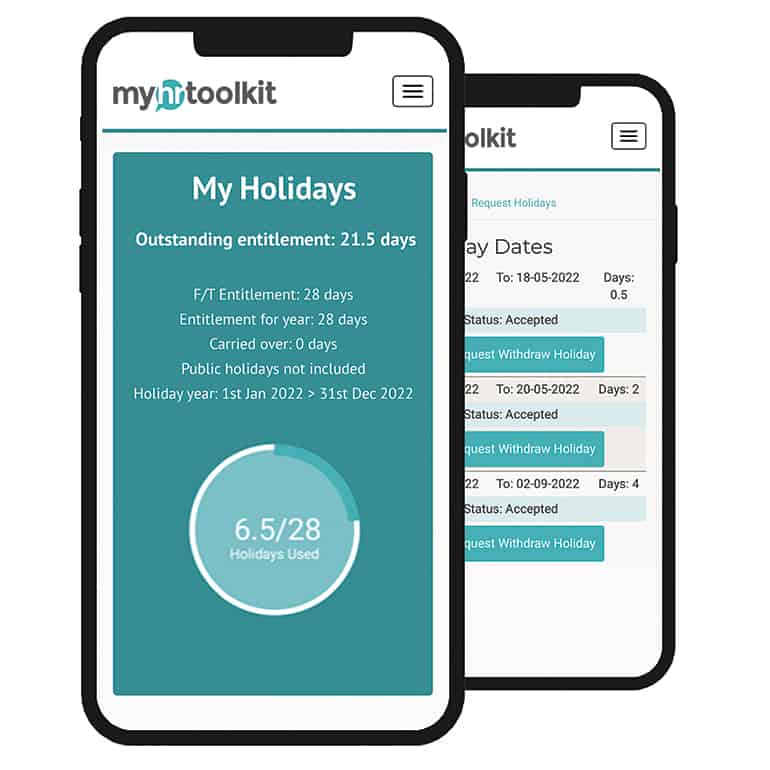 Mobile
Mobile